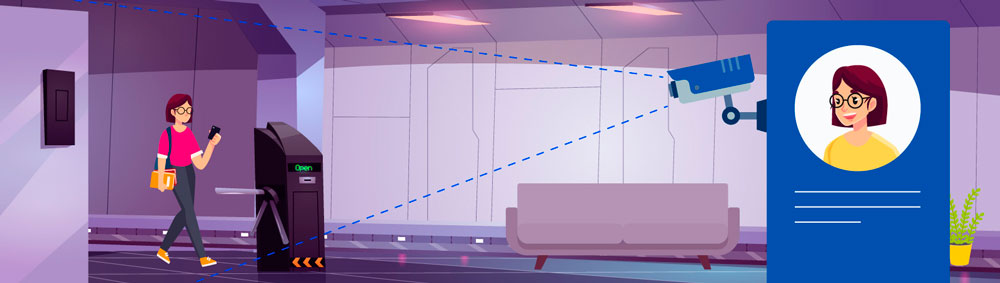
People tend to lose their passcards or leave them unattended, which complicates the process of going through the turnstile or the doors in secure buildings. Their key-card might have been left at home or the office. Therefore, in order to pass the Access Control System (ACS), they have to call security and probably spend quite some time facing a closed door.
The solution we are offering is to use our recognition module to identify the face of a person approaching the door. It eliminates the need to constantly carry the passcard with you and worry if you have forgotten to take it with you.
How does our face recognition system work?
-
Step 1: The IP camera is installed right next to the door.
-
Step 2: The camera sends a video stream to the server where visitors approaching the door are recognized.
-
Step 3: At the moment of recognition, Flussonic Watcher sends a request to the ACS integration module, which requests access from the ACS server.
-
Step 4: The ACS server makes a decision and sends a command to the controller to unlock the door.
Thus, people who are authorized to enter, and only the people who are authorized, can automatically go through the door or turnstile without having a personal passcard.
Our solution includes:
- Watcher Server
- Video card for video analytics
- IP-camera aimed at eye level or with a deviation of no more than 15 degrees along the horizon with HD / FullHD resolution. Face size - at least 10% of the frame height
- ACS server
- ACS controller for controlling the actuator
- ACS reader for card access, in case the face is not recognized
- Actuating device - lock or turnstile
- Push to exit button (if an electromagnetic lock is used) or a second reader (if a turnstile is used)
- Integration script
Application Areas
The solution further optimizes the checkpoints of enterprises, increasing the throughput of access points, as well as simplifying the work of the security service. Another obvious advantage is the ability of the ACS to view the list of recognition events with face screenshots, date, and time of recognition. You can open a list of visitors with photos, names, and personal IDs at any time. You no longer have to worry about losing your access card. All you need to take with you is your face.