Many managers suppose they do not have to do anything with their own hands because assistants and secretaries can “volunteer” and carry out any assignment for them. On top of that, some employees benefit from shifting the responsibility onto their co-workers. These irresponsible actions often lead to financial transactions being performed by unverified employees. The most vulnerable sector is the bank sphere.
- Secretaries perform various financial transactions for millions of dollars, using their boss’s hardware keys.
Obviously, such a loophole provokes fraudulent schemes involving illegal transfers of large sums of money. As an example, there is a case where a bank employee stole over 13 thousand dollars from his clients. In the period from December 2019 to January 2020, the man used information constituting a commercial secret and stole money from client accounts seven times! Unfortunately, this is far from the only time when bank employees have illegally used access rights to their own advantage.
In these kinds of situations, the verification of the user will help you ensure the security of financial operations.
How does Flussonic verify users?
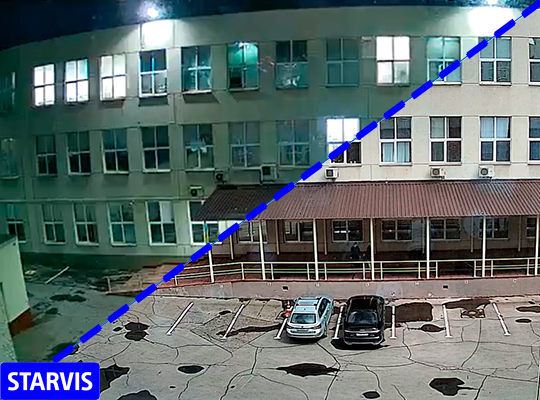
With an IP or web camera installed in close proximity to the computer that has access to financial accounts (the camera is added to Flussonic Watcher as an RTSP stream), just like in the spy movies. While sitting at the computer, an employee initiates transactions by logging in to the database using a hardware security key or digital signature. Immediately after authorization, the system sends a request to Watcher. Watcher, in turn, compares the time when the recognition event occurred with the time the operation was performed.
Further, there are two options for events:
- If the recognition time matches the person’s ID received from Watcher, the transaction is confirmed.
- Otherwise, the transaction is blocked, and corresponding notification is sent to security services.
Solution
- Watcher Server
- Video card for video analytics
- IP or web-camera aimed at the user sitting in front of the computer with HD / FullHD resolution. Face size - at least 10% of the frame height
- Accounting system server
- Hardware security key or digital signature
A user verification system can be installed in banks, insurance companies, and other organizations where access for transactions with a hardware security key or a digital signature is required. Moreover, the solution will allow you to verify customers. Verification using personal recognition will help avoid illegal transactions, fraud, and increase the security of financial transactions.